The usual person in the tech industry will inevitably have a storage medium you “must” secure before letting it out of your possession. This could mean something as simple as a personal drive with financial records, personal projects, and embarrassing photos that made their way to Facebook anyway.
First, these opinions are my own, and I am not a data destruction expert. Take this as you will, but do your due diligence for your needs or wants. Do not use my advice if you are representing the government, a financial service, a publicly held company, or a health care organization. There are legal penalties for failure to sanitize data using specific methods for your entity.
See “Tutorial on Disk Drive Data Sanitization” by Gordon Huges, UCSD CMMR and Tom Coughlin for great in-depth information from UC San Diego.
Spinning Platter and SSD Hard Drives
You’ve probably seen multiple-pass wipe methods corresponding to National Industrial Security Program Operating Manual (NISPOM) methods or Cognizant Security Authority data sanitization standards used by the CSA (DoD, DoE, NRC, and CIA).
However, for most of us, that’s total overkill. If you own a drill and don’t want to resell, reuse, or gift it, just drill a few holes in it, throw it on the concrete, and drop it off at a recycling facility that will send it through a shredder anyway.
If you do wish to keep it usable, multiple pass wipes are probably not necessary as you’re talking about magnetic force microscope recovery methods where its theoretically possible 25 years ago to recover data on disk drives with storage capacities measured in Megabytes. Today we have capacities in Gigabytes and Terabytes, even Petabytes in rare cases.
But you do have to consider that software wipes can miss bad tracks or sectors; therefore, hardware shredding is the ultimate option. Tracks that have been remapped due to failures may contain chunks of data that will not be touched by overwrite attempts. Typically these are genuinely bad, and data is not retrievable. This is a small risk.
DiskPart Clean
The DiskPart “clean all” command removes any partition or volume formatting from the drive. Only the MBR partitioning and hidden sector information are altered on master boot record (MBR) discs. The GPT partitioning information, including the Protective MBR, is rewritten on GUID partition table (GPT) discs; there is no hidden sector information. It also specifies that each sector on the drive is zeroed (secure erase), erasing all data on the disc completely. The data on the disc will be realistically unrecoverable due to this. Running the “clean all” command on a drive will take roughly an hour for 320 GB.
Note, the following commands will erase/clean your drive permanently. Use with care!
- Run command prompt
- Run
diskpart - Run
list disk - Note your disk number. You can find additional information on what disk numbers are by running the “Disk Management” UI tool.
- Run
select disk #(replace # with the noted disk number) - Run
cleanall
Note: This command will work with SSD drives, but reduces their lifespan more quickly.
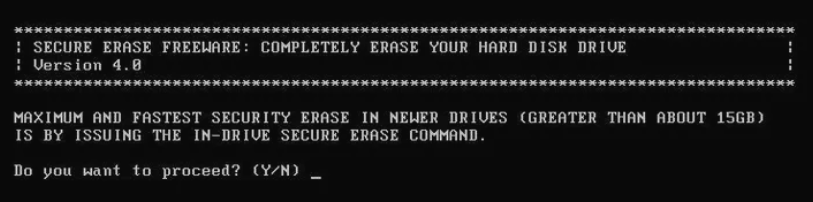
HDDErase
This method is just as free but requires an application download from the Internet.
Secure Erase is the name given to a set of commands available from the firmware on PATA and SATA-based hard drives (it isn’t available on SCSI drives).
According to lifewire.com, “Using Secure Erase to erase the data from a hard drive is often considered the best way to do so because the action is accomplished from the drive itself, the same hardware that wrote the data in the first place. Other erasing methods may be less effective because they rely on more standard ways of overwriting it.
According to the National Institute of Standards and Technology Special Publication 800-88, the only method of software-based data sanitation must utilize a hard drive’s Secure Erase commands.”
The NSA worked with the Center for Magnetic Recording Research at the University of California, San Diego, to research hard drive data sanitation. A result of that research was HDDErase, a freely available data destruction software program that works by executing the Secure Erase commands.
Secure erase data sanitization writes a binary one or zero. No verification of the overwrite is needed because the writing occurs from within the drive, meaning the drive’s write fault detection prevents any misses. This makes Secure Erase faster than other data sanitization methods and arguably more effective.
HDDErase is a data destruction program. You download a .zip package that includes the executable and a bootable ISO. You can also create any boot media you want (floppy, disc, flash drive, etc.) and copy the HDDERASE.EXE file or burn the ISO to a bootable medium. The included text file, HDDEraseReadMe.txt, has some information on how to create the boot disk.
Because this program runs before the operating system is loaded, it can erase any operating system and even the one you’re primarily using, like whatever you have running on the C: drive.
DOWNLOAD SECURE ERASE
from the Center for Memory and Recording Research at UC San Diego.
For an excellent usage overview and screenshots of the program, see HDDErase v4.0 Review from lifewire.com. This version was created in 2008.